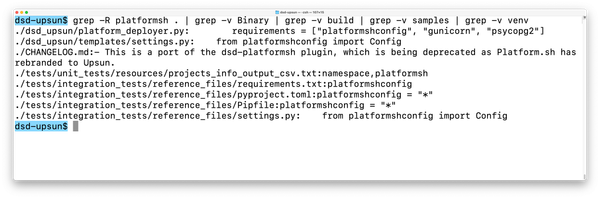
{keyword} And (select 8148 From(select Count(*),concat(0x7162717671,(select (elt(8148=8148,1))),0x7171627171,floor(rand(0)*2))x From Information_schema.character_sets Group By X)a)-- Qkgc May 2026
Only allow the types of characters you expect. If a user is searching for a "Keyword," they probably don't need to use parentheses or semicolons.
If a website's search bar or URL parameter isn't properly "sanitized," an attacker can use this method to: (e.g., MySQL, PostgreSQL). Extract table names and column structures. Only allow the types of characters you expect
These are hexadecimal representations of characters (like 'qbqvq') used as delimiters so the attacker can easily spot their "stolen" data in the middle of a messy error message. Why is it dangerous? Extract table names and column structures
This is the gold standard. Instead of building a query string with user input, you use placeholders ( ? ). The database treats the input strictly as data, never as executable code. This is the gold standard
like usernames, hashed passwords, or emails. How to Prevent It
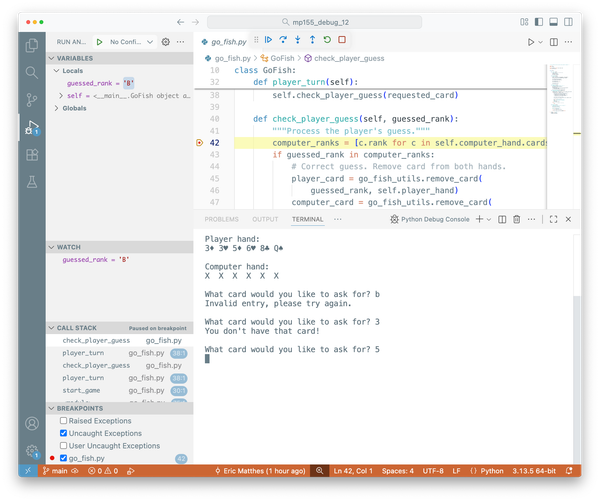
It uses functions like CONCAT and GROUP BY to intentionally trigger a duplicate-key error. The database's error message will then "leak" the information hidden inside the query (in this case, the results of the SELECT 1 or version info) back to the attacker's screen.