Download — File Cute Slim Girlfriend.zip
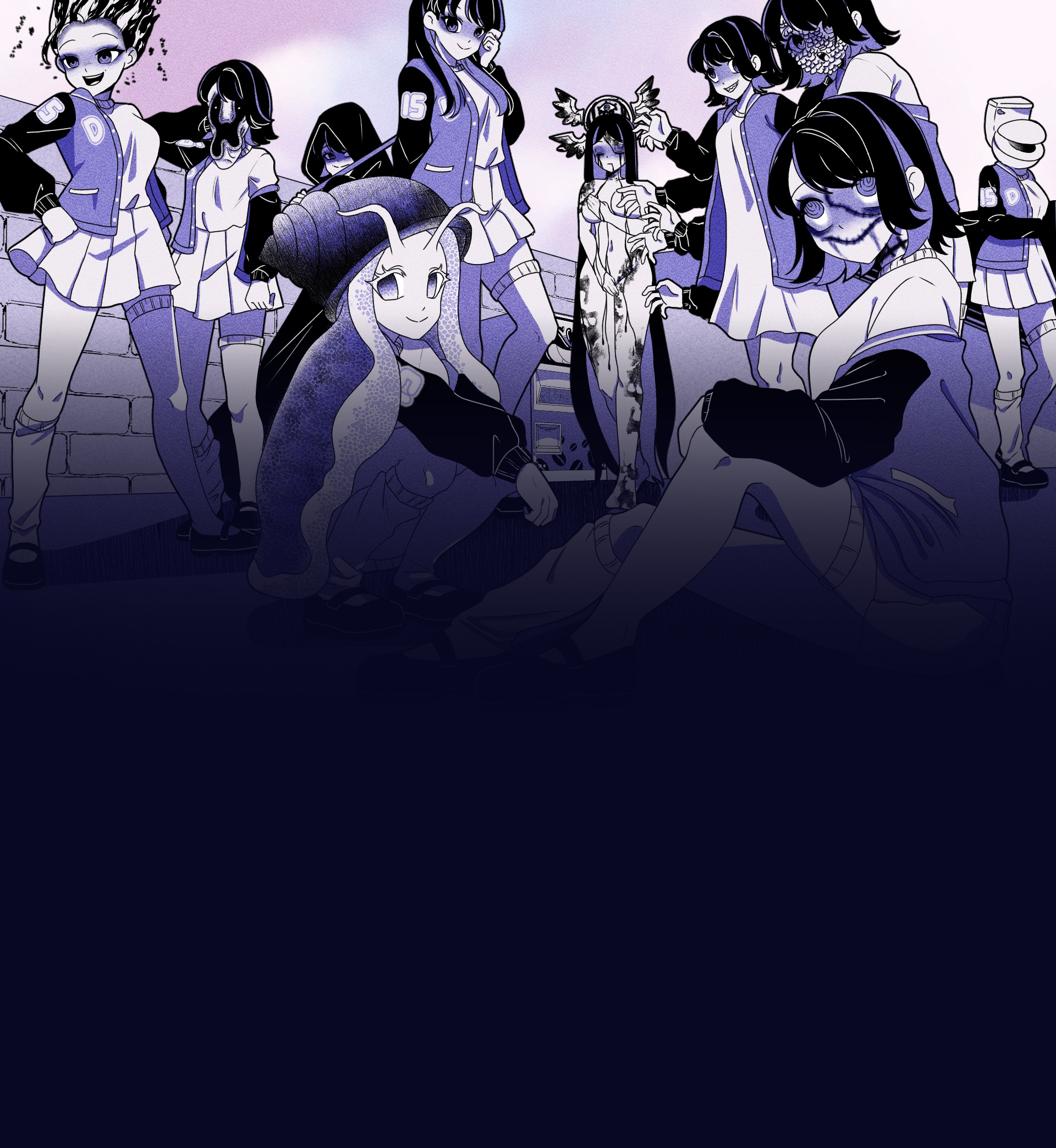
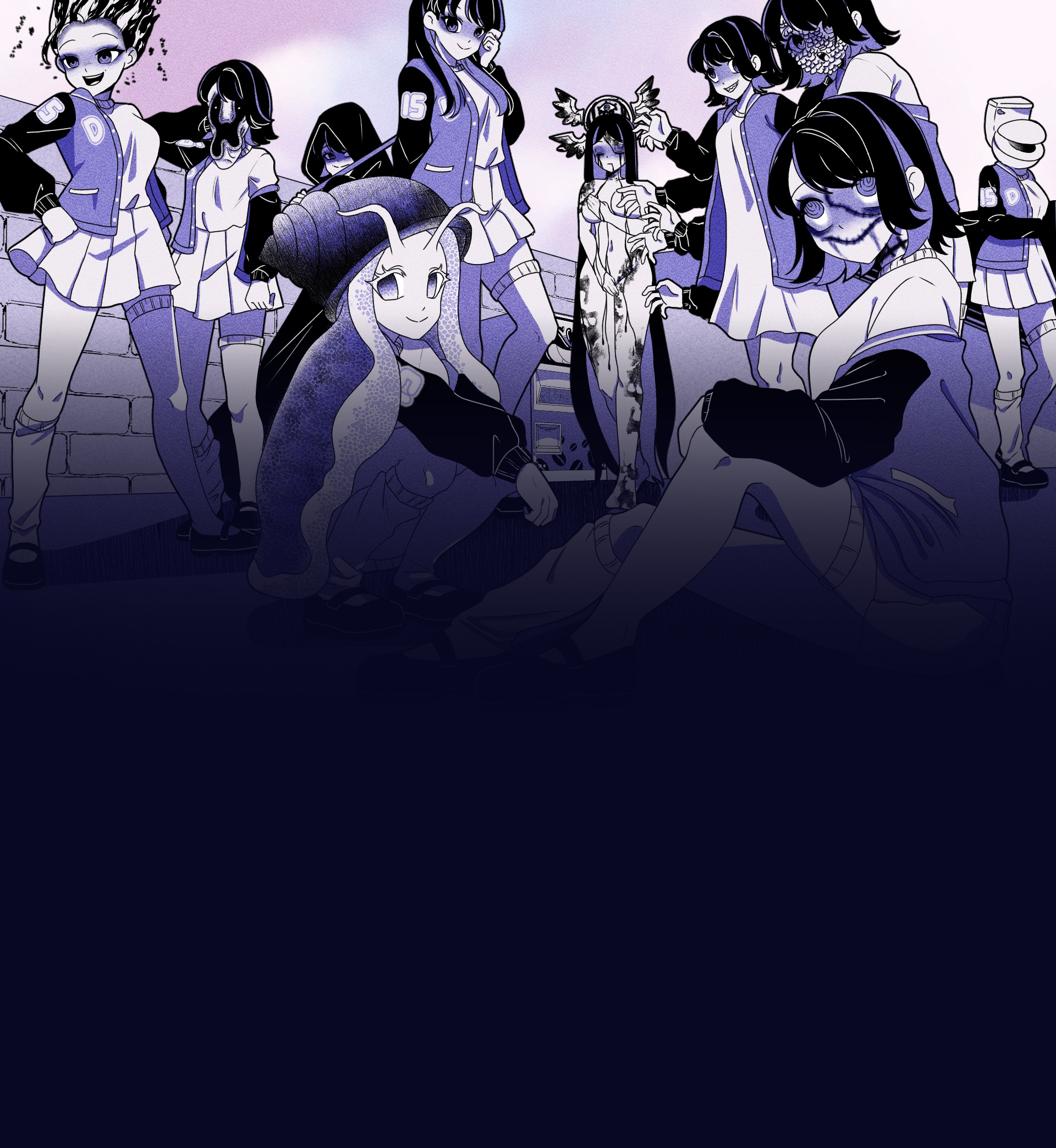
A unique visual novel where you explore a mysterious coffee machine that can dispense any liquid imaginable
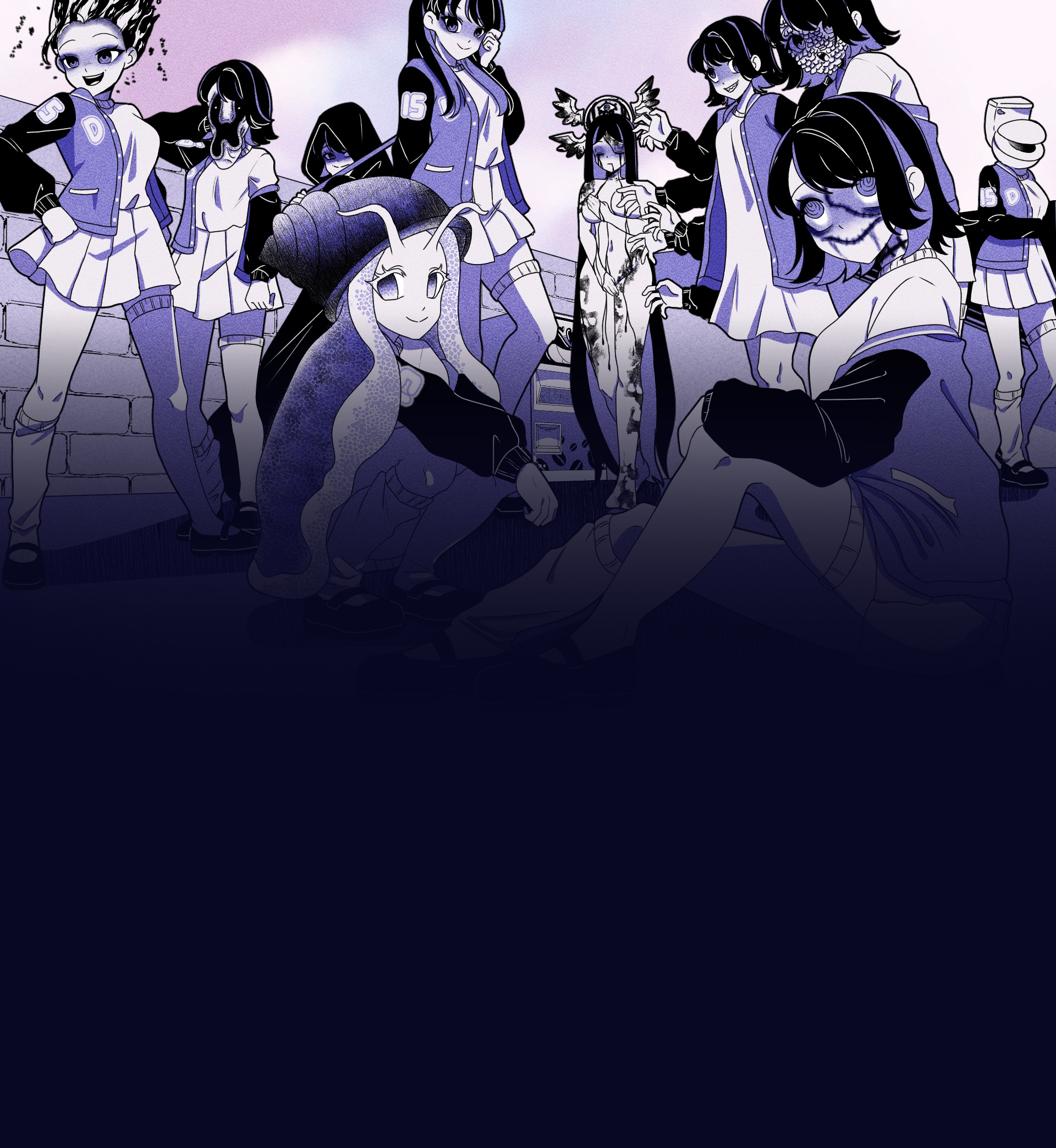
A unique visual novel where you explore a mysterious coffee machine that can dispense any liquid imaginable
Experience this unique visual novel interactive simulation game directly in your browser. No downloads required!
Click the button below to load and start the game Download File Cute slim girlfriend.zip
Visual Novel
30-60 minutes
Single Player
Web Browser
: If the "folder" is only a few kilobytes (KB), it is likely a script rather than a collection of media files.
: Inside the ZIP, there is often a hidden .exe , .scr , or .vbs file disguised with a fake icon (like a photo or folder icon) to trick you into running code.
: Use a reputable antivirus or anti-malware tool (like Windows Defender, Malwarebytes, or Bitdefender) to ensure no background processes were triggered.
: The title targets emotional or curiosity-driven impulses. By promising specific "cute" content, attackers hope the user will ignore security warnings to see the file's contents.
: Ensure your file explorer is set to "Show file extensions." Often, a file named image.jpg is actually image.jpg.exe . How to Identify Malicious Downloads
Discover what makes Anomalous Coffee Machine an unforgettable gaming experience
Interact with a mysterious vending machine that can dispense any liquid imaginable, possible or impossible.
Type in any word you can think of and see if the machine can dispense it. Endless possibilities await.
Experience a wide range of transformations and effects based on what you choose to drink.
Enjoy a rich visual experience with numerous animated scenes and visual effects.
Immerse yourself in an extensive narrative with over 100,000 words of dialogue and story content.
Interact with a mysterious girl who guides you through the experience of the anomalous machine.
: If the "folder" is only a few kilobytes (KB), it is likely a script rather than a collection of media files.
: Inside the ZIP, there is often a hidden .exe , .scr , or .vbs file disguised with a fake icon (like a photo or folder icon) to trick you into running code.
: Use a reputable antivirus or anti-malware tool (like Windows Defender, Malwarebytes, or Bitdefender) to ensure no background processes were triggered.
: The title targets emotional or curiosity-driven impulses. By promising specific "cute" content, attackers hope the user will ignore security warnings to see the file's contents.
: Ensure your file explorer is set to "Show file extensions." Often, a file named image.jpg is actually image.jpg.exe . How to Identify Malicious Downloads