Atomic-email-hunter-15-20-0-485-crack-with-serial-key-free-download -
Our mission is to improve the design process for architects and engineers. By improving the comfort of work, using a fast and intuitive interaction with the software.
GET NOW
Our mission is to improve the design process for architects and engineers. By improving the comfort of work, using a fast and intuitive interaction with the software.
GET NOW
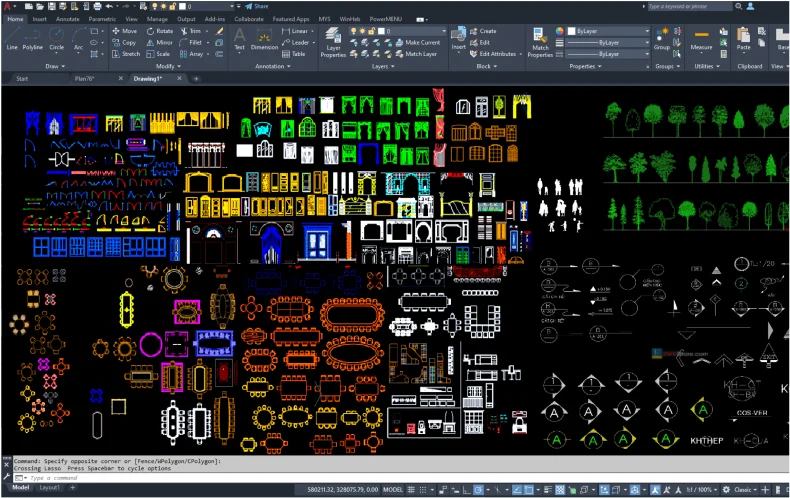
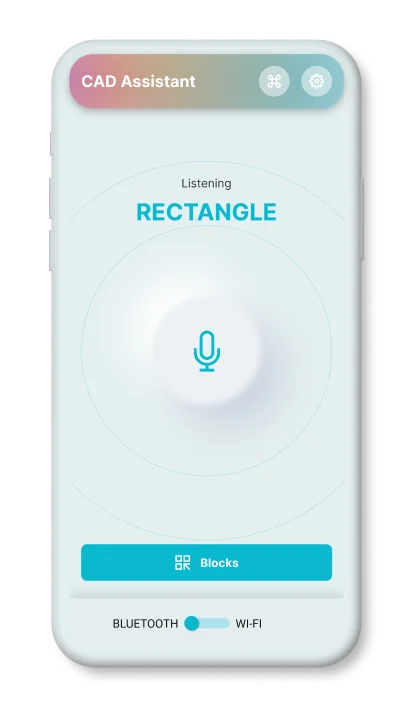
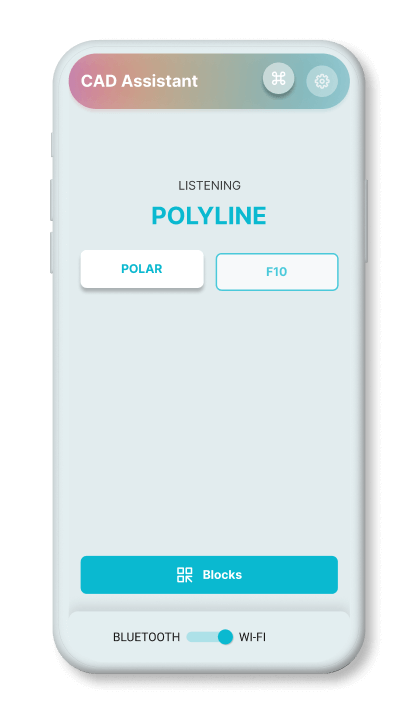
a mobile application that can execute the user's voice commands in AutoCAD










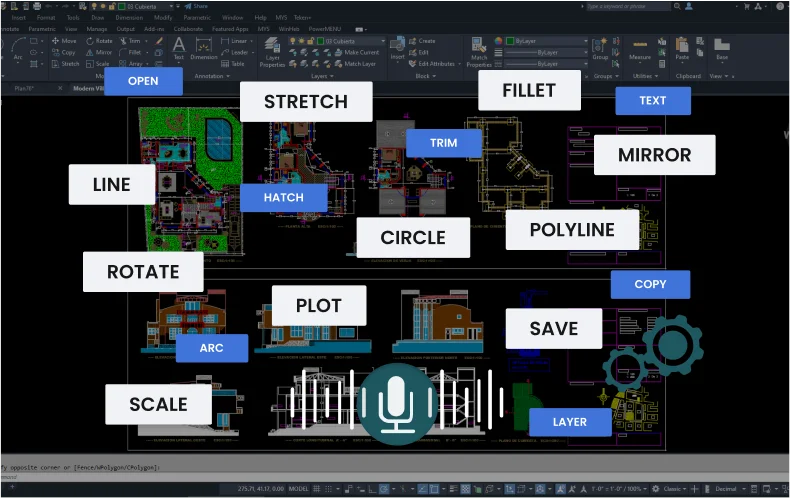
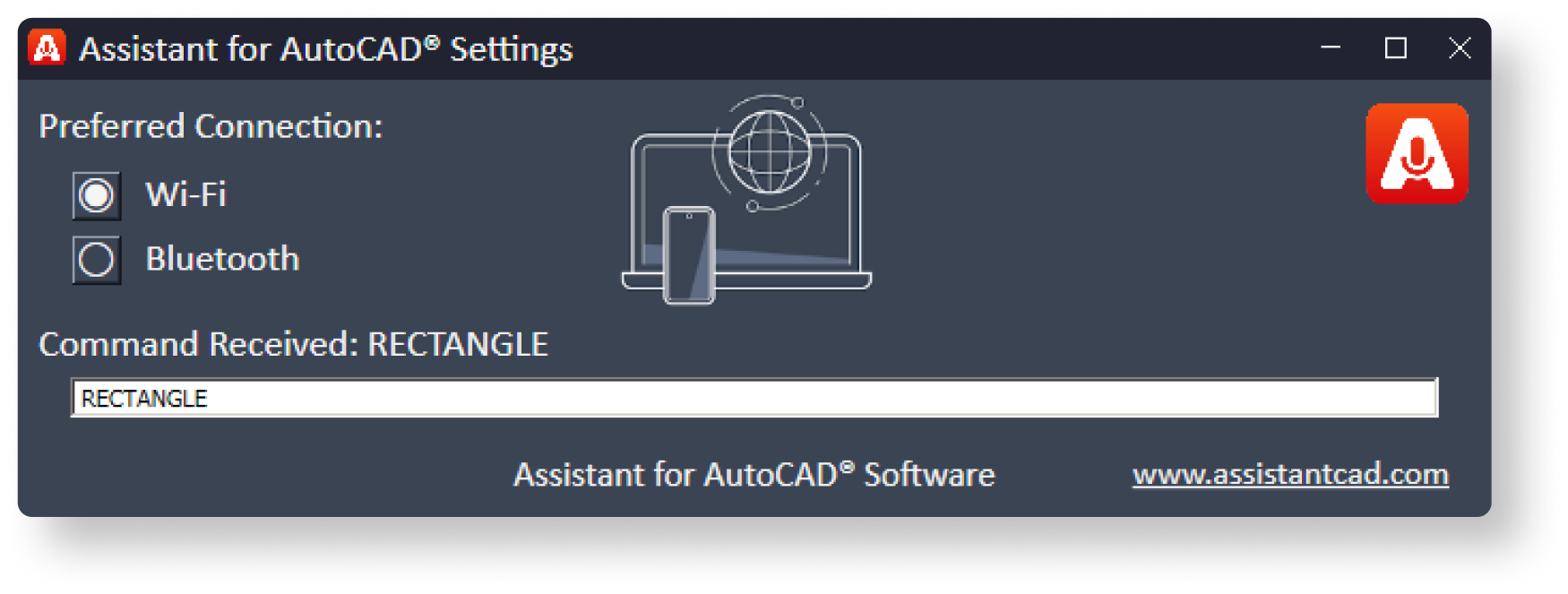
Works via Wi-Fi
runs in the background
Works via Bluetooth
Supports operation
via a headset (audio)
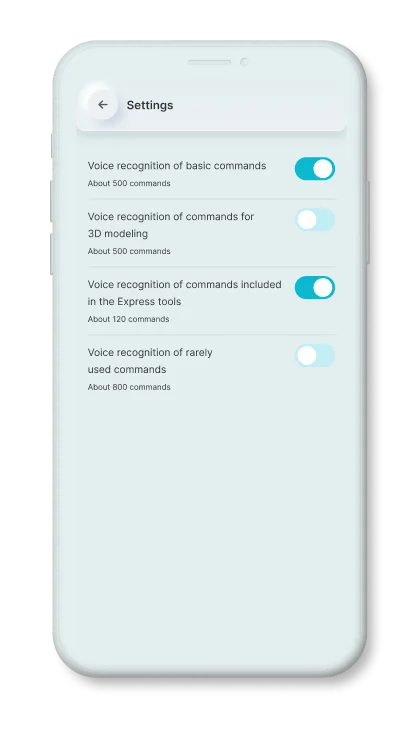
Basic commands
that are used most often.
Express
tool commands.
Commands
for 3d modeling.
Rarely used
AutoCAD commands

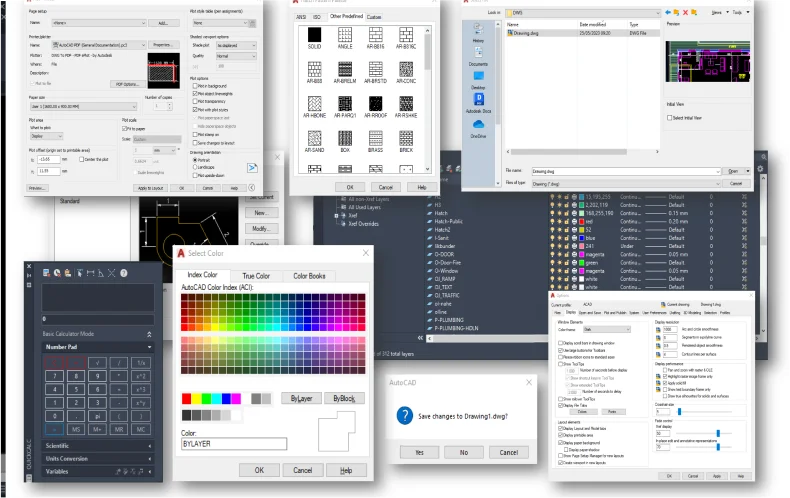
The first tool to manually improve the commands, for this he needs to record the command in his voice.
In this way, the engine will know and take into account the individual peculiarities of the pronunciation of the given command.
1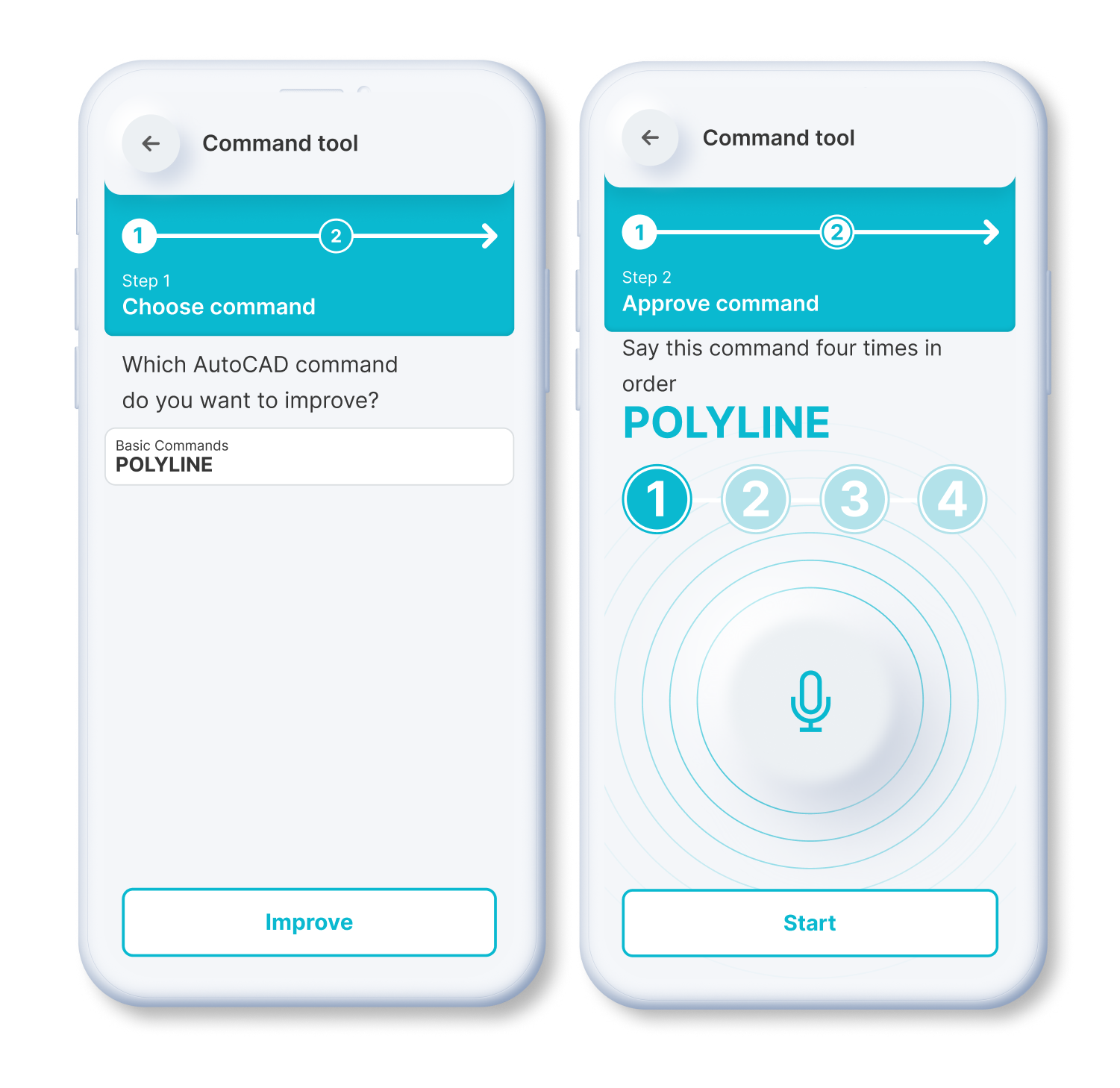
If the recognition engine algorithm is not confident in determining the correct command, it will offer to choose from the appropriate options.
The application then saves the user's choice, and will take that result into account at a later time. In this way, the engine is fine-tuned to the individual peculiarities of pronunciation.
2Static Blocks
Dynamic Blocks
Simply speak a command to
resize or scale items.
Rapidly rotate objects or elements within the application by precisely 90 degrees.
By issuing a voice command, you can activate the mirroring effect.
You can effortlessly rotate blocks or objects within the application.
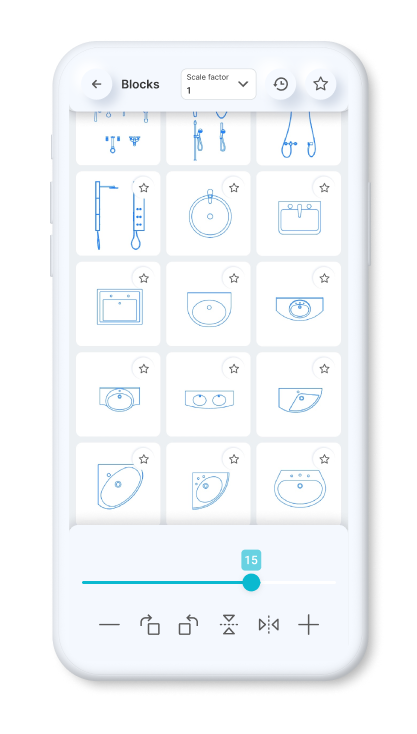
You can set a constant scale factor for your drawings to enter blocks.
Save the blocks you want most in your favorites.
Use the history page to quickly insert the last used blocks.
Standardized American
paper sizes A, B, C, D, E
Two special vertical
formats for A3 and A4

The international paper size standard is ISO 216 A4, A3, A2, A1, A0
Architectural sizes C, D, E
As John continued to investigate, he stumbled upon a blog post from a cybersecurity expert who warned about the dangers of downloading pirated software. The expert explained that cracked versions often came bundled with malware, which could compromise a user's system and steal sensitive information.
It was a typical Monday morning for John, a digital marketing specialist, as he sipped his coffee and scrolled through his inbox. However, his day took an unexpected turn when he stumbled upon an intriguing email with the subject line: "Atomic Email Hunter 15.20.0.485 Crack with Serial Key Free Download". The email was from an unknown sender, and the content seemed too good to be true. As John continued to investigate, he stumbled upon
John's experience with Atomic Email Hunter served as a reminder to his colleagues and friends about the risks associated with pirated software. He shared his story with them, emphasizing the importance of prioritizing cybersecurity and respecting intellectual property. However, his day took an unexpected turn when
As a result, John's team began to adopt more stringent security measures, and their overall awareness of potential threats increased. They also started to explore alternative, legitimate solutions for their email marketing needs, which ultimately led to more effective and sustainable results. He shared his story with them, emphasizing the
Curious, John opened the email and began to read. The message claimed that Atomic Email Hunter was a powerful tool for extracting email addresses from various sources, and that the cracked version with a serial key was available for free download. The email also promised that the software would help John "dominate the email marketing landscape" and "boost his online business to new heights".
The experience taught John a valuable lesson about the importance of prioritizing cybersecurity and respecting intellectual property. He also discovered that Atomic Email Hunter was a powerful tool, but one that required a legitimate license to use safely and effectively.
In the end, John's quest for Atomic Email Hunter had become a journey of discovery, one that had taught him to be more cautious and informed in his pursuit of digital tools and solutions.